Biography
Giovanni Pecoraro is a Senior Security Engineer at RHEA Group. His research interests include space systems, cyber security, signal processing and artificial intelligence.
- Space Systems
- Cyber Security
- Signal Processing
- Machine Learning
- Deep Learning
PhD in Electronic Engineering, 2019
University of Roma "Tor Vergata" - Roma, Italy
MEng in Advanced Communication and Navigation Satellite Systems, 2016
University of Roma "Tor Vergata" - Roma, Italy
MSc in Telecommunications Engineering, 2013
University of Napoli "Federico II" - Napoli, Italy
BSc in Telecommunications Engineering, 2011
University of Napoli "Federico II" - Napoli, Italy
Skills
Experience
Recent Posts
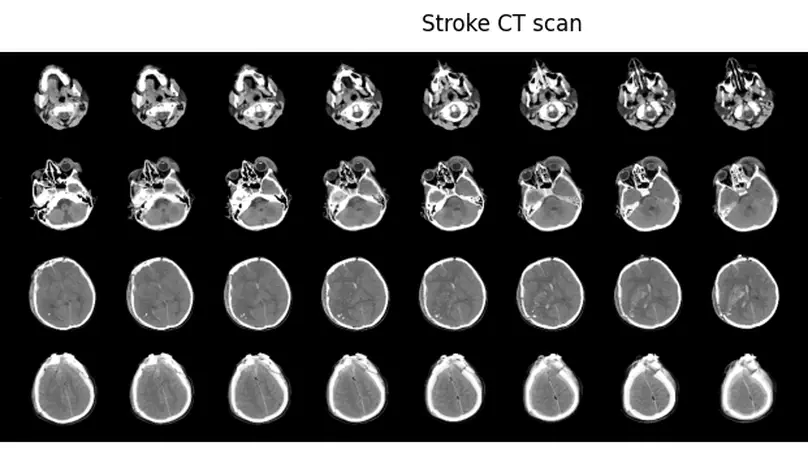
A tutorial on how to train a 3D Convolutional Neural Network (3D CNN) to detect the presence of brain stroke from Computer Tomography (CT) scans.

A key step towards the application of Deep Learning to medical images is the understanding of Digital Imaging and Communications in Medicine (DICOM) which represents the standard for the communication and management of medical imaging.
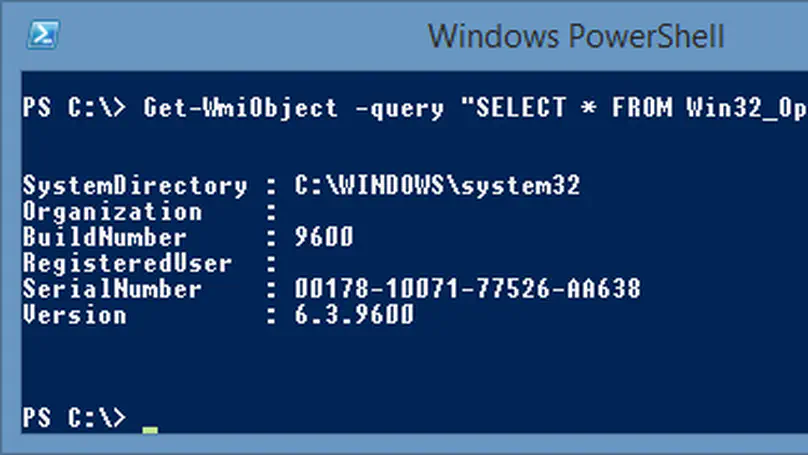
Windows Management Instrumentation (WMI) provides a unique interface to manage a local or remote network or computer and thus can be used by both Red and Blue Teams.

MSSQL Servers integrate right out the box with Windows and Active Directory Domains. Consequently, there are trust relationships wich we can be leveraged from an attacker perspective.
Projects
Featured Publications
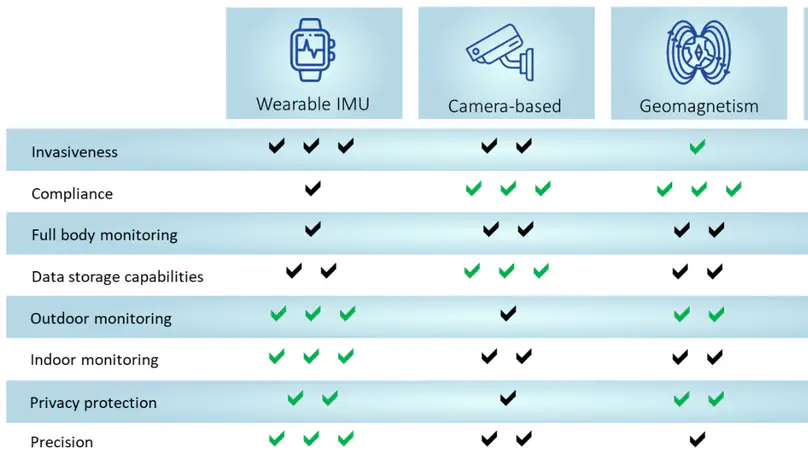
Different technologies have been proposed for indoor monitoring over the past decades, with different degrees of invasiveness, complexity, and capabilities in full-body monitoring. In recent years, among all available technologies, there has been an increasing interest in using RF-based technology because it can provide a more accurate and reliable method of tracking patients’ movements compared to other methods, such as camera-based systems or wearable sensors.
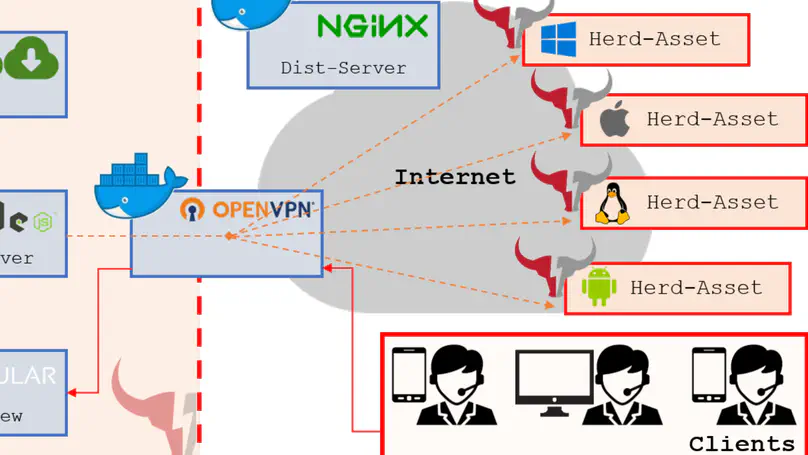
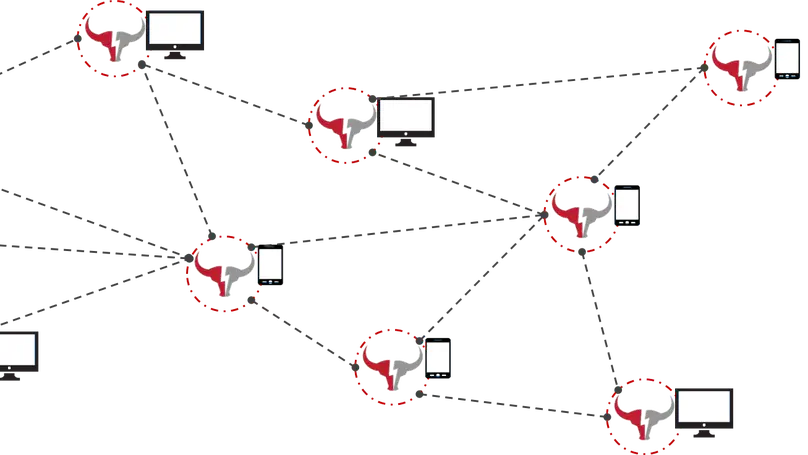
Nowadays, time, scope and cost constraints along with knowledge requirements and personnel training constitute blocking restrictions for effective Offensive Cyberspace Operations (OCO). This paper presents RedHerd, an open-source, collaborative and serverless orchestration framework that overcomes these limitations. RedHerd leverages the ‘as a Service’ paradigm in order to seamlessly deploy a ready-to-use infrastructure that can be also adopted for effective simulation and training purposes, by reliably reproducing a real-world cyberspace battlefield in which red and blue teams can challenge each other. We discuss both the design and implementation of the proposed solution, by focusing on its main functionality, as well as by highlighting how it perfectly fits the Open Systems Architecture design pattern, thanks to the adoption of both open standards and wide-spread open-source software components. The paper also presents a complete OCO simulation based on the usage of RedHerd to perform a fictitious attack and fully compromise an imaginary enterprise following the Cyber Kill Chain (CKC) phases.
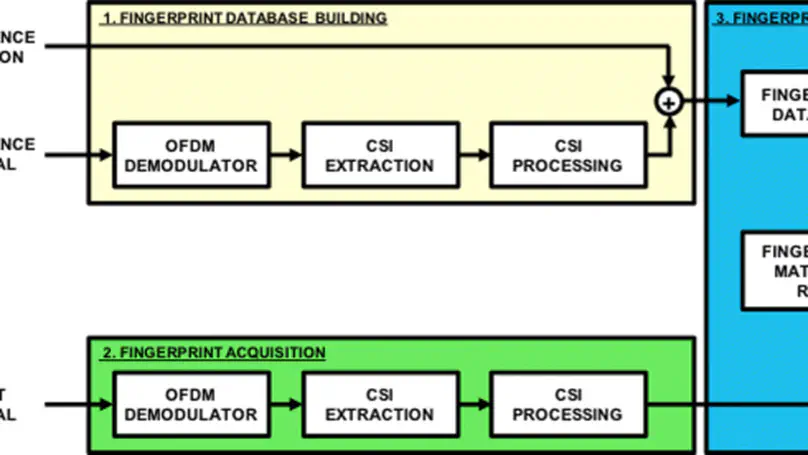
This paper addresses the use of channel state information (CSI) for Long Term Evolution (LTE) signal fingerprinting localization. In particular, the paper proposes a novel CSI-based signal fingerprinting approach, where fingerprints are descriptors of the “shape” of the channel frequency response (CFR) calculated on CSI vectors, rather than direct CSI vectors. Experiments have been carried out to prove the feasibility and the effectiveness of the proposed method and to study the impact on the localization performance of (i) the bandwidth of the available LTE signal and (ii) the availability of more LTE signals transmitted by different eNodeB (cell diversity). Comparisons with other signal fingerprinting approaches, such as the ones based on received signal strength indicator or reference signal received power, clearly show that using LTE CSI, and in particular, descriptors as fingerprints, can bring relevant performance improvement.